What is the Social Engineering Toolkit? [Complete Guide]
What is SET?
A useful set of tools for social engineering is integrated into one Python-based tool called the Social Engineer Toolkit (SET). It is frequently used by penetration testers or Red Team members to evaluate an organization’s security by imitating social engineering attacks on personnel. It is also useful for practicing purposes for cyber security students or learners.
SET provides a wide range of methods for attacking, including website cloning, malicious payloads, spear phishing, and infectious media creation. Such attacks are resilient and hard to defend against because they take advantage of the human-level weaknesses from which an organization cannot escape
What is Social Engineering?
![image What is the Social Engineering Toolkit? [Complete Guide]](https://cyberodisha.com/wp-content/uploads/2024/09/image.png)
Social engineering is a cognitive ploy used to influence individuals into disclosing private information or performing specific tasks instead of employing technological techniques to obtain unwanted access to private information. It depends on taking advantage of individual feelings, reliability, and fascination
In simple terms Social Engineering is to trick people by manipulating them into sharing their sensitive information either by picking on their emotions, poking them psychologically, or bothering them to an extent where they are persuaded to share their sensitive information.
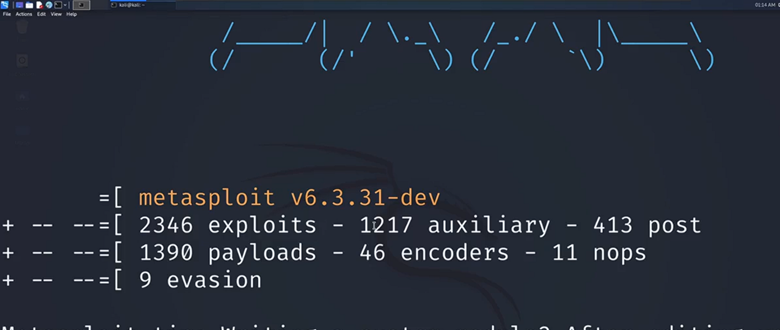
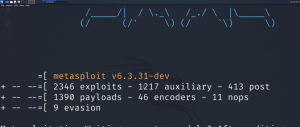
Installation
The Social Engineer Toolkit already comes pre-installed in Kali. To start SET, simply head to your terminal and type: sudo setoolkit
Or, to download SET, type the following command in Linux:
git clone https://github.com/trustedsec/social-engineer-toolkit
Tools and Options:
![image-1 What is the Social Engineering Toolkit? [Complete Guide]](https://cyberodisha.com/wp-content/uploads/2024/09/image-1.png)
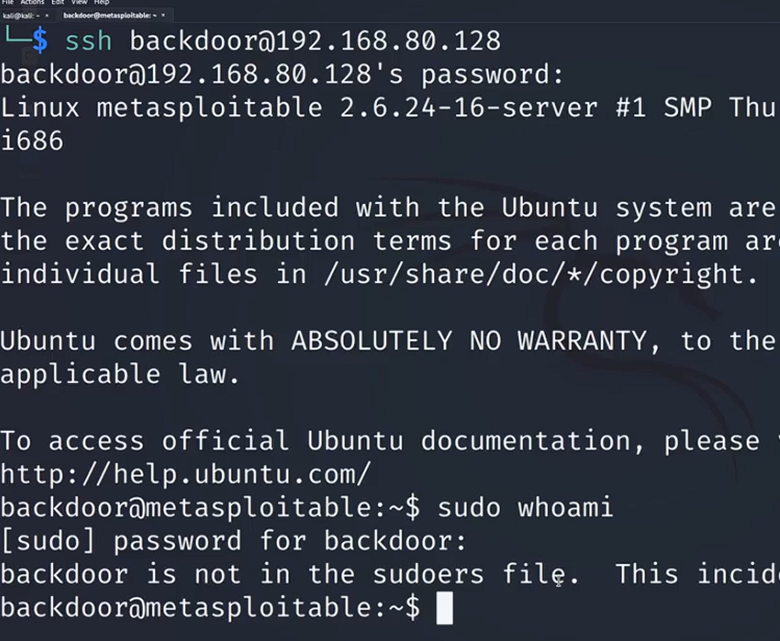
1) Social-Engineering Attacks:
![image-2 What is the Social Engineering Toolkit? [Complete Guide]](https://cyberodisha.com/wp-content/uploads/2024/09/image-2.png)
This option focuses on different attack vectors used in social engineering, such as website attacks, spear phishing, generating ubiquitous media, and credential harvesting. Users can use it to test and simulate various human behavior-based attack scenarios.
1) Penetration Testing (Fast-Track):
![image-3 What is the Social Engineering Toolkit? [Complete Guide]](https://cyberodisha.com/wp-content/uploads/2024/09/image-3.png)
Fast-Track is a set of scripts and testing tools developed to swiftly identify vulnerabilities and take advantage of security flaws. It expedites the process of identifying and taking benefit from loopholes and assists in automating several penetration testing activities.
2) Third Party Modules:
![image-4 What is the Social Engineering Toolkit? [Complete Guide]](https://cyberodisha.com/wp-content/uploads/2024/09/image-4.png)
Integration with third-party tools and modules created by the security community is offered via this option. The capabilities of SET are expanded by these modules, which may additionally offer more payloads, exploits, and attack routes for the toolkit.
3) Update the Social-Engineer Toolkit:
By using this option, you may upgrade SET to the most recent version and ensure you have the latest version with the newest features, bug fixes, and other enhancements. Updating your toolkit regularly is crucial to keeping it functional and trustworthy.
4) Update SET Configuration:
One can edit the SET configuration file using this option.
5) Help, Credits, and About:
This option gives you access to the Social Engineer Toolkit’s help manuals, developer and contributor credit information, and general details. It is an ideal location to find details regarding the toolkit’s creation history, receive help, and comprehend how it works
Conclusion:
There are many more options available for every individual option mentioned above. We can utilize the diverse and potent tools from the invaluable Social Engineer Toolkit (SET ) for phishing, harvesting credentials, and website cloning emphasizing the significance of knowledge and caution when it comes to internet security.
It is always important to use these tools mindfully and utilize them only for security research and learning.
- Iran–Israel Cyber Conflict 2026: Hacktivist Activity, Cyber Threat Landscape, and Global Impact Analysis
- Why Python for Ethical Hacking?
- Asian Heart Institute Data Leak 2026: Serious Dark Web Exposure of 120GB Sensitive Hospital Data
- WiZiX Technology Group Data Leak 2026: Major Dark Web Breach Puts Sensitive Data at Risk
- Raymundos Food Group Data Leak 2026: Shocking Dark Web Breach Exposes Confidential Files






Post Comment