Why Python for Ethical Hacking?
Advantages of Using Python in Cybersecurity
Python has become one of the most popular programming languages for ethical hacking and cybersecurity due to its numerous advantages:
- Ease of Learning and Use: Python’s simple and readable syntax
makes it easy for beginners to learn and for experienced programmers
to write code quickly.
# Example of Python's readable syntax
for i in range(5):
print(f"This is iteration {i}"- Versatility: Python can be used for various tasks, from simple scripting to complex application development, making it suitable for different aspects of ethical hacking.
- Large Standard Library: Python comes with a comprehensive standard library that provides many built-in modules for common tasks, reducing the need for external dependencies.
import os
import sys
import socket
# Using built-in modules for system operations and
networking
print(f"Current directory: {os.getcwd()}")
print(f"Python version: {sys.version}")
print(f"Hostname: {socket.gethostname()}")- Extensive Third-Party Libraries: Python has a vast ecosystem of third-party libraries specifically designed for cybersecurity and ethical hacking tasks.
- Cross-Platform Compatibility: Python code can run on various operating systems, making it ideal for testing in different environments.
- Rapid Prototyping: Python’s interpreted nature allows for quick testing and iteration of ideas, which is crucial in the fast-paced field of cybersecurity.
- Integration Capabilities: Python can easily integrate with other languages and tools commonly used in cybersecurity, enhancing its versatility.
- Strong Community Support: The large and active Python community provides extensive resources, documentation, and support for cybersecurity professionals.
Why Python for Ethical Hacking?
Python offers numerous libraries that are particularly useful for ethical hacking and cybersecurity tasks. Here are some of the most popular ones:
Why Python for Ethical Hacking?
from scapy.all import IP, TCP, sr1
# Sending a TCP SYN packet to a target
target_ip = "192.168.1.1"
target_port = 80
syn_packet = IP(dst=target_ip) / TCP(dport=target_port,
flags="S")
response = sr1(syn_packet, timeout=2, verbose=False)
if response and response.haslayer(TCP):
if response[TCP].flags == 0x12: # SYN-ACK
print(f"Port {target_port} is open")
elif response[TCP].flags == 0x14: # RST-ACK
print(f"Port {target_port} is closed")
else:
print(f"No response received for port {target_port}")Requests: A user-friendly HTTP library for making web requests and interacting with web applications.
import requests
# Sending a GET request to a website
url = "https://example.com"
response = requests.get(url)
print(f"Status Code: {response.status_code}")
print(f"Headers: {response.headers}")
print(f"Content: {response.text[:100]}...") # First 100
characters of contentBeautiful Soup: A library for parsing HTML and XML documents,useful for web scraping and data extraction.
import requests
from bs4 import BeautifulSoup
# Scraping a website for links
url = "https://example.com"
response = requests.get(url)
soup = BeautifulSoup(response.text, 'html.parser')
links = soup.find_all('a')
for link in links:
print(f"Link: {link.get('href')}")Paramiko: A library for implementing the SSH2 protocol, allowing secure remote connections and file transfers.
import paramiko
# Establishing an SSH connection
ssh = paramiko.SSHClient()
ssh.set_missing_host_key_policy(paramiko.AutoAddPolicy())
try:
ssh.connect('example.com', username='user',
password='password')
stdin, stdout, stderr = ssh.exec_command('ls -l')
print(stdout.read().decode())
finally:
ssh.close()Nmap: A Python library for network discovery and security auditing, wrapping the functionality of the Nmap security scanner.
import nmap
# Performing a simple port scan
nm = nmap.PortScanner()
nm.scan('192.168.1.1', '22-80')
for host in nm.all_hosts():
print(f"Host: {host}")
for proto in nm[host].all_protocols():
print(f"Protocol: {proto}")
ports = nm[host][proto].keys()
for port in ports:
state
= nm[host][proto][port]['state']
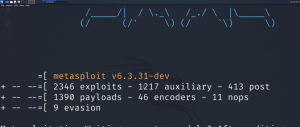
print(f"Port {port}: {state}")Pymetasploit3: A Python library for interacting with the Metasploit Framework, useful for automating penetration testing tasks.
from pymetasploit3.msfrpc import MsfRpcClient
# Connecting to Metasploit RPC and listing available
exploits
client = MsfRpcClient('password', port=55553)
exploits = client.modules.exploits
print("Available exploits:")
for exploit in exploits:
print(exploit)These libraries, along with many others, provide ethical hackers with powerful tools to perform various security testing and analysis tasks efficiently.






Post Comment