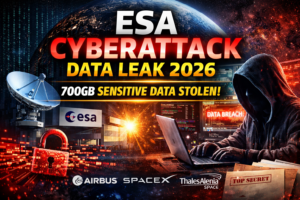
ESA Cyberattack Data Leak 2026: 700GB Massive Breach Reveals Critical Space Secrets
Introduction: ESA Cyberattack Data Leak
The ESA cyberattack data leak has become one of the most serious cybersecurity incidents in the global space sector. In January 2026, the European Space Agency officially confirmed that it suffered multiple cyberattacks, leading to the leakage of hundreds of gigabytes of sensitive internal data.
Even though ESA clarified that its mission-critical and classified systems were not compromised, experts believe the breach still poses long-term strategic risks. In today’s digital world, even “unclassified” engineering data can give attackers a roadmap of how critical infrastructure works.
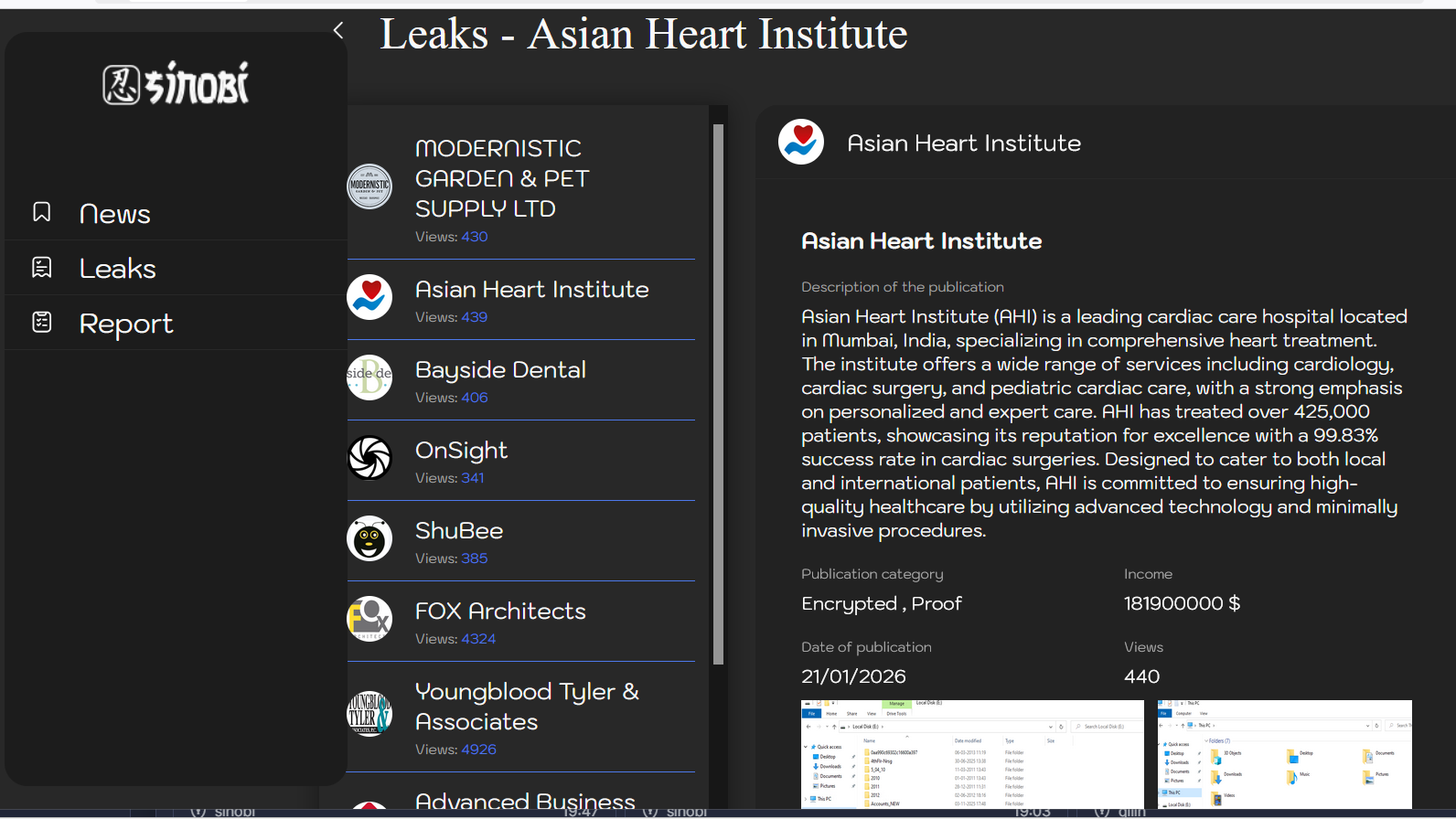
What Happened in the ESA Cyberattack Data Leak
According to ESA’s public statement, the breach happened across a small set of external science servers. These systems were mainly used for collaborative engineering and research with external partners. However, attackers managed to stay inside the environment for several days, quietly extracting data.
This ESA cyberattack data leak did not occur in a single incident but rather through two separate breaches, raising serious questions about patch management and access monitoring.
Who Were the Attackers and How Big Was the Breach
Two different threat actors claimed responsibility:
- A hacker using the alias “888” claimed to have stolen around 200 GB of data in late December 2025.
- Shortly after, a group calling itself “Scattered Lapsus$ Hunters” claimed a second breach, allegedly extracting 500 GB more data by exploiting an unpatched security vulnerability.
In total, the ESA cyberattack data leak is estimated to involve nearly 700 GB of data, making it one of the largest leaks ever reported in the aerospace sector.
What Kind of Data Was Stolen
Reports suggest that the stolen data includes:
- Proprietary internal software
- API keys and access tokens
- Hardcoded credentials
- Engineering and mission documentation
Some leaked files reportedly contain references to major aerospace partners such as Airbus, SpaceX, and Thales Alenia Space.
While no classified mission data was confirmed as leaked, the exposure of credentials and internal logic is a serious red flag.
Impact on ESA and the Global Space Ecosystem
ESA stated that its core corporate network and classified systems remain secure. However, cybersecurity experts warn that the ESA cyberattack data leak could still have indirect consequences:
- Attackers can study system architecture
- Credentials may be reused elsewhere
- Supply-chain partners could be targeted
- Future attacks may become easier
For space agencies, even minor leaks can translate into national security and economic risks.
How the Hackers Entered ESA Systems
Initial analysis indicates that attackers gained access to development platforms such as Jira and Bitbucket. These platforms often store sensitive configuration files, scripts, and access credentials.
Experts believe the attackers maintained a foothold for nearly a week, which suggests gaps in log monitoring and anomaly detection. The presence of unpatched vulnerabilities played a major role in enabling the ESA cyberattack data leak.
ESA’s Official Response and Investigation
ESA confirmed that it has:
- Launched a criminal investigation
- Informed and is cooperating with relevant authorities
- Is conducting forensic analysis on compromised devices
- Has isolated affected systems
This incident also follows a 2024 breach of ESA’s official web shop, where malicious code was used to harvest credit card information, showing a pattern of increasing cyber threats.
Why Even “Unclassified” Data Is Dangerous
Many people assume that unclassified data is harmless, but that is not true. In the case of the ESA cyberattack data leak, unclassified engineering documents can still expose:
- Internal workflows
- Technology dependencies
- Infrastructure blueprints
Such information can be used for future espionage or sabotage.
Lessons for Organisations and Governments
This incident offers key takeaways:
- Patch management is non-negotiable
- Development platforms must be secured like production systems
- Credential scanning should be automated
- Zero-trust access models are essential
For Indian organisations working with government or defence projects, the ESA cyberattack data leak is a clear warning.








Post Comment