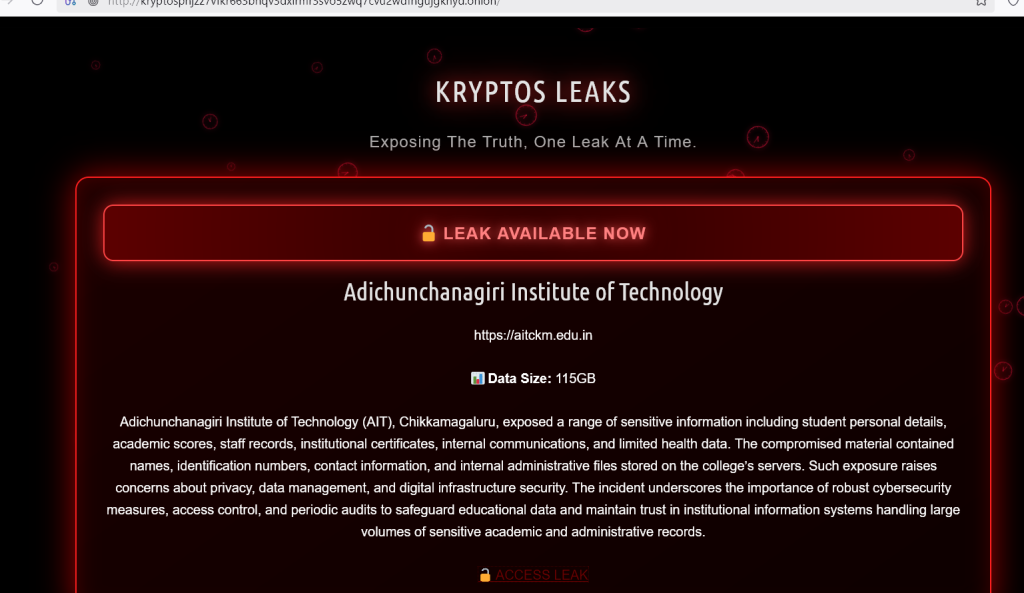
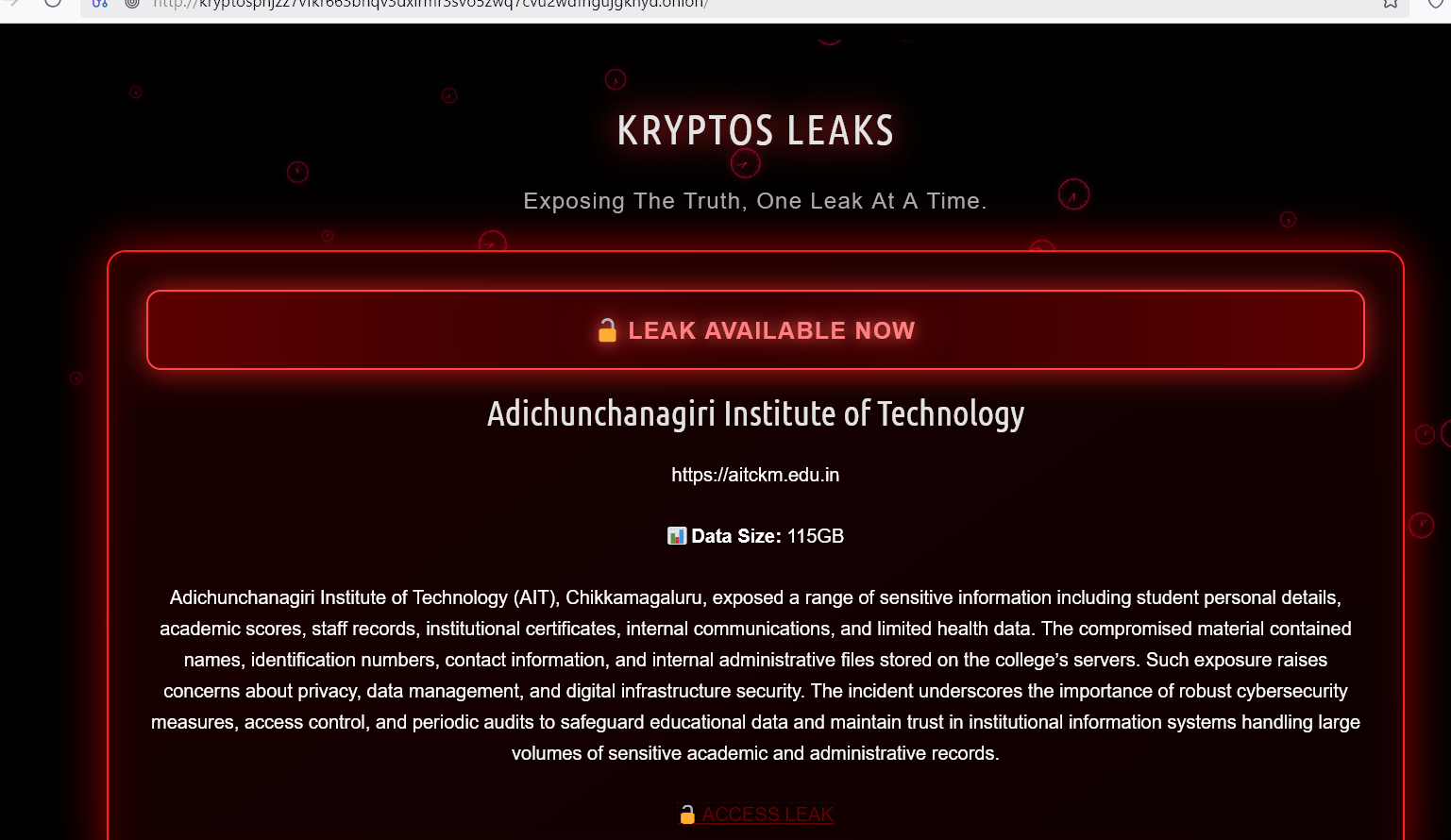
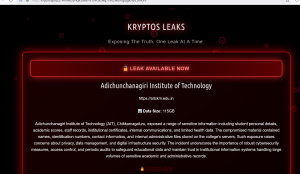
Data Exposure at Adichunchanagiri Institute of Technology (AIT) Chikkamagaluru — Reported Kryptos Leak
Published: October 24, 2025 (incident date reported)
Data Published: 04 November 2025
Source domain: aitckm.edu.in
Alleged threat actor: Kryptos Group
User-reported leak size: 115 GB (provided by requester)
Allegations of the Leaked Information
According to reports from multiple threat-intelligence trackers, the ransomware/ extortion group Kryptos claimed responsibility for an incident affecting Adichunchanagiri Institute of Technology (AIT), Chikkamagaluru, and posted that the institute’s data was exfiltrated and will be released unless demands are met. Public trackers and daily ransomware summaries identified AIT (domain: aitckm.edu.in) as a Kryptos victim on or about 24 October 2025.
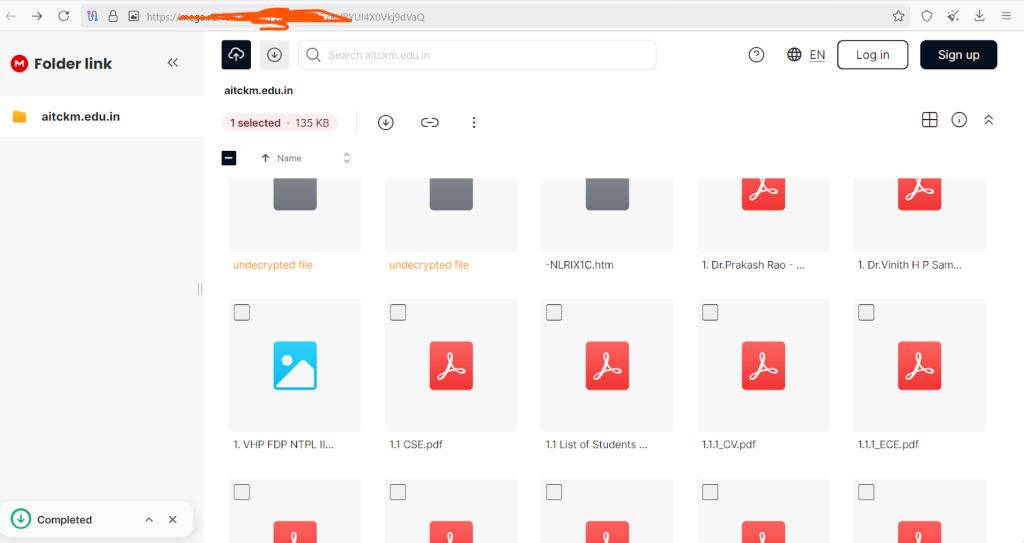
The material described in your brief and corroborated by the pattern of such leaks includes: student personal details (names, IDs, contact information), academic records and scores, staff records, institutional certificates, internal administrative files and limited health data. You report the dataset size as 115 GB; this volume — if accurate — would be consistent with a large collection of academic and administrative records spanning multiple years and departments. (Note: public reporting on the incident identifies the attack and the actor, but does not confirm the full contents or the 115 GB size in open sources at the time of writing.)
Disclaimer
This article is a synthesis based on: (a) the incident signals and writeups visible on open cyber-intelligence trackers and ransomware observatories, (b) the AIT public website for institutional context, and (c) the data description you supplied (including the 115 GB figure). Where public sources and your submission disagree or where public sources provide no specific detail (for example, exact file lists or verifiable data volume), I have explicitly noted that the detail comes from your report. This write-up does not assert forensic certainty about file-level contents or the chain of custody of leaked files — only that the group Kryptos publicly claimed the incident and that threat-intel feeds listed AIT as a victim on 24 Oct 2025.
Summary
- Who: Adichunchanagiri Institute of Technology (AIT), Chikkamagaluru (domain: aitckm.edu.in). Adichunchanagiri Institute of Technology
- When: Public reporting and threat-actor postings date the claim to 24 Oct 2025.
- What: A claimed data exfiltration by the Kryptos group; reported categories include student and staff PII (personal identifiable information), academic scores, administrative documents, some health records and internal communications. You report a 115 GB dataset.
- Why it matters: Educational institutions store sensitive personal and academic records; exposure can harm students, staff and institutional reputation, enable identity fraud, and create regulatory and compliance liabilities. Large volumes of educational data have been repeatedly targeted in 2025, reflecting a persistent threat to the sector.
Advisory (Immediate steps for affected parties)
If you are a student, staff member, or administrator at AIT, consider the following actions immediately:
- Assume passwords may be compromised. Reset passwords for institutional accounts and any other accounts that reuse the same credentials. Use unique, strong passwords and enable multi-factor authentication (MFA) wherever possible.
- Monitor for identity misuse. Watch bank/UPI/card statements, emails, and phone/SMS for signs of phishing, fraud, or SIM/social-engineering attempts. Report suspicious financial activity immediately to your bank and local law enforcement.
- Check academic verification pathways. If certificates or marksheets are part of the leak, be prepared for fraudulent verification requests. Institutions and employers should verify documents through official channels (e.g., university portals, authenticated transcripts), not only via emailed copies.
- Be cautious with communications. Attackers often follow breaches with targeted phishing (spear-phishing) using leaked context. Do not click links or open attachments from unexpected emails. Verify senders independently.
- Legal and regulatory: The institute should assess applicable data-protection obligations (state/national laws) and notify regulators and affected individuals as required by law and institutional policy. Engage legal counsel experienced in data-breach response.
Further Approach (For the Institute / IT Team / External Responders)
- Isolate and preserve evidence. Immediately isolate affected systems, preserve logs, and collect forensic images for investigation. Avoid altering suspected compromised systems before evidence capture.
- Engage third-party incident responders. Engage an experienced IR (incident response) firm to perform forensic triage, identify exfiltration vectors (e.g., RDP, VPN, vulnerable web app, stolen credentials, or misconfigured cloud storage), and validate the scope.
- Perform a full credential reset and least-privilege review. Force password resets, revoke stale accounts, rotate service credentials and API keys, and audit privileged access.
- Remediate technical root causes. Patch vulnerable services, harden remote access (VPN/MFA), review backups for integrity, and ensure offline/immutable backups exist to enable recovery without paying ransoms.
- Communications plan. Prepare transparent, factual notifications to students, staff, regulators, and partners that explain what is known, what steps are being taken, and guidance for individuals to protect themselves.
- Longer-term: Implement regular security audits, penetration testing, staff security training, data minimization and encryption at rest, and improved logging/monitoring to detect future intrusions earlier.
Conclusion
The reported Kryptos claim against Adichunchanagiri Institute of Technology highlights the growing risk to educational institutions holding large volumes of sensitive records. Whether the dataset is exactly 115 GB (as you report) or somewhat smaller, the operational and human impact is real: students and staff face potential privacy and fraud risks, and the institute faces legal, reputational and operational challenges.
Immediate protective actions (password resets, monitoring, and careful communication) combined with a properly resourced forensic response and long-term security investments are the correct path forward. The incident also underlines a sector-wide need for better cybersecurity hygiene, resilient backups, and incident preparedness in education.







Post Comment